In this article:
Step 1. Preparing Domain Environment
Setting Up Domain/Integrated Domain Authentication in Linux OS
To set up domain or integrated domain authentication on Apache2 web server in Linux OS using PostgreSQL DBMS, follow the steps below.
TIP. It is recommended to set up simultaneous use of domain/integrated domain authentication with built-in authorization.
Step 1. Preparing Domain Environment
Foresight Analytics Platform gets information about domain security subjects from the domain catalog service or global catalog that must be set up in the computer network. Interaction with the directory service is executed via the LDAP/LDAPS protocol.
If the catalog service of the current domain (global catalog of the current network) is based on Active Directory, and Foresight. Analytics Platform works in Windows OS, advanced settings do not need to be determined to connect to this service.
If the directory service is located at Linux OS server, or it is required to connect to the directory service in the network other than the current one (Linux or Windows OS server), execute the following operations depending on the operating system in use:
Install necessary packages depending on Linux OS version:
Debian-based distributions:
sudo apt install libldap-2.4-2 libsasl2-modules-gssapi-mit
RedHat-based distributions:
sudo yum install openldap openldap-clients
ALT Linux:
sudo apt-get install openldap-common
Download and run the OpenSSL installer. The default installation folder for OpenSSL: C:\Program Files\OpenSSL-Win64.
Add the path to the bin folder - C:\Program Files\OpenSSL-Win64\bin to the PATH system variable.
Preparing domain environment also includes:
Installation and setup of Kerberos PostgreSQL DBMS server. Make sure that domain information is added in the /etc/krb5.conf file. For details see Kerberos documentation.
Creation of keytab files and setup of services: postgres for domain authentication; HTTP, postgres for integrated domain authentication. Keytab files are used to authenticate users without entering password in Astra Linux Directory (ALD) in Linux OS or Active Directory (AD) in Windows OS. A Keytab file stores names of Kerberos principals and corresponding encrypted keys obtained based on Kerberos passwords.
NOTE. If user properties are changed, keytab file should be recreated.
Step 2. Setting Up BI Server
NOTE. When setting up domain authentication skip this step.
When installing BI server, configuration files of the Apache2 instance are located in the folder by default:
/etc/apache2-fp10.x in Debian-based distributions.
/etc/httpd-fp10.x in RedHat-based distributions.
/etc/httpd2-fp10.x in ALT Linux.
To set up BI server:
Install necessary packages depending on Linux OS version:
Debian-based distributions:
sudo apt install libsasl2-modules-gssapi-mit libapache2-mod-auth-gssapi
RedHat-based distributions:
sudo yum install cyrus-sasl-gssapi mod_session mod_auth_gssapi
ALT Linux:
sudo apt-get install apache2-mod_auth_gssapi libsasl2-plugin-gssapi
Copy configuration files of Apache2 web server to the Apache2 instance with BI server:
Debian-based distributions:
cp /etc/apache2/mods-available/auth_gssapi.load /etc/apache2-fp10.x/mods-available/
cp /etc/apache2/mods-available/session.load /etc/apache2-fp10.x/mods-available/
cp /etc/apache2/mods-available/session_cookie.load /etc/apache2-fp10.x/mods-available/
RedHat-based distributions:
cp /etc/httpd/conf.modules.d/01-session.conf /etc/httpd-fp10.x/conf.modules.d/
cp /etc/httpd/conf.modules.d/10-auth_gssapi.conf /etc/httpd-fp10.x/conf.modules.d/
ALT Linux:
cp /etc/httpd2/conf/mods-available/auth_gssapi.load /etc/httpd2-fp10.x/conf/mods-available/
cp /etc/httpd2/conf/mods-available/session.load /etc/httpd2-fp10.x/conf/mods-available/
cp /etc/httpd2/conf/mods-available/session_cookie.load /etc/httpd2-fp10.x/conf/mods-available/
Enable the missing Apache2 modules in Debian-based distributions and in ALT Linux:
a2enmod-fp10.x auth_gssapi
a2enmod-fp10.x authz_user
a2enmod-fp10.x authn_core
a2enmod-fp10.x headers
a2enmod-fp10.x session
a2enmod-fp10.x session_cookie
a2enmod-fp10.x rewrite
a2enmod-fp10.x setenvif
Enable the mod_request.so unit in RedHat-based distributions. Uncomment the string in the /etc/httpd-fp10.x/conf.modules.d/00-base.conf file:
LoadModule request_module modules/mod_request.so
Change the configuration file of BI server fp10.x-biserver.conf located in the folder:
/etc/apache2-fp10.x/mods-available in Debian-based distributions.
/etc/httpd-fp10.x/conf.d in RedHat-based distributions.
/etc/httpd2-fp10.x/conf/mods-available in ALT Linux.
Cats the file contents to the following view:
# Foresight AnalyticsPlatform
LoadModule axis2_module "/opt/foresight/fp10.x-biserver/bin/libmod_axis2_2_4.so"
Axis2RepoPath "/opt/foresight/fp10.x-biserver/bin"
Axis2LogFile "/opt/foresight/fp10.x-biserver/var/log/axis2.log"
Axis2LogLevel info
Axis2ServiceURLPrefix services
<Location /FPBI_App_v10.x/axis2>
SetHandler axis2_module
Require valid-user
AuthType GSSAPI
GssapiAllowedMech krb5
GssapiCredStore keytab:<path to keytab file for HTTP service>
GssapiDelegCcacheDir /opt/foresight/fp10.x-biserver/var/cache
GssapiUseSessions On
<IfModule mod_session.c>
Session on
</IfModule>
<IfModule mod_session_cookie.c>
SessionCookieName gssapi_sessionpath=/;httponly;secure;
</IfModule>
</Location>
The file contains path to main files of BI server located in the /opt/foresight/fp10.x-biserver folder by default.
After executing the operations the BI server is set up.
In Active Directory one can use unlimited and limited delegation:
To use unlimited delegation, select the Trust This User for Delegation to Any Service (Kerberos only) radio button on the Delegation tab in user properties.
To use limited delegation:
Select the Trust This User for Delegation to Specified Services Only > Use Any Authentication Protocol radio button on the Delegation tab in user properties.
Append the BI server configuration file fp10.x-biserver.conf in the <Location> section. Enable the GssapiUseS4U2Proxy option and specify additional parameters:
GssapiUseS4U2ProxyOn
GssapiCredStore client_keytab:<path to keytab file for HTTP service>
GssapiCredStore ccache:FILE:/opt/foresight/fp10.x-biserver/var/cache/krb5ccache
Astra Linux Directory uses unlimited delegation.
Step 3. Setting Up Domain/Integrated Domain Authentication
To set up domain/integrated domain authentication:
Set up two repository connections in the Metabases.xml file:
When domain authentication is used:
For administrator, repository connection parameters should contain the Authentication attribute that is set to 1.
For domain users, repository connection parameters should contain the Authentication attribute that is set to 4.
The example of the Metabases.xml file:
<PP>
<Metabases>
<REPOSITORY_ID Name="WAREHOUSE" Authentication="1" Driver="POSTGRES" Package="STANDARDSECURITYPACKAGE">
<LogonData DATABASE="DATABASE_NAME" SERVER="SERVER_DATABASE" CASESENSITIVE="true"/>
</REPOSITORY_ID>
<REPOSITORY_ID_DOMAIN Name="WAREHOUSE_DOMAIN" Authentication="4" Driver="POSTGRES" Package="STANDARDSECURITYPACKAGE">
<LogonData DATABASE="DATABASE_NAME" SERVER="SERVER_DATABASE" CASESENSITIVE="true"/>
</REPOSITORY_ID_DOMAIN>
</Metabases>
</PP>
When integrated domain authentication is used:
For administrator, repository connection parameters should contain the Authentication attribute that is set to 1.
For domain users, repository connection parameters should contain the Authentication attribute that is set to 2.
The example of the Metabases.xml file:
<PP>
<Metabases>
<REPOSITORY_ID Name="WAREHOUSE" Authentication="1" Driver="POSTGRES" Package="STANDARDSECURITYPACKAGE">
<LogonData DATABASE="DATABASE_NAME" SERVER="SERVER_DATABASE" CASESENSITIVE="true"/>
</REPOSITORY_ID>
<REPOSITORY_ID_INT_DOMAIN Name="WAREHOUSE_INT_DOMAIN" Authentication="2" Driver="POSTGRES" Package="STANDARDSECURITYPACKAGE">
<LogonData DATABASE="DATABASE_NAME" SERVER="SERVER_DATABASE" CASESENSITIVE="true"/>
</REPOSITORY_ID_INT_DOMAIN>
</Metabases>
</PP>
Determine full domain DNS name of server:
In the SERVER parameter in the /opt/foresight/fp10.x-biserver/etc/Metabases.xml file.
In the serviceUrl and baseUrl parameters in the /opt/foresight/fp10.x-webserver/r/config/config.json file.
In the PP_SOM variable in the /etc/opt/foresight/fp10.x-webserver/envvars file.
For Apache2 web server specify the ServerName parameter inside the <VirtualHost> tag in the file:
/etc/apache2-fp10.x-web/sites-available/webserver.conf in Debian-based distributions.
/etc/httpd-fp10.x-web/conf.d/00-virtualhost.conf in RedHat-based distributions.
/etc/httpd2-fp10.x-web/conf/sites-available/000-default.conf in ALT Linux.
Set the parameters of comparison between directory service attributes and security subject attributes in Foresight Analytics Platform and specify user credentials to connect to the directory service in the settings.xml file. If required, connect additional controllers for domains or subdomains.
Restart BI server and web application back end.
Add domain users and/or groups in the security manager.
After executing the operations the domain/integrated domain authorization is set up.
Step 4. Preparing DBMS Server
To prepare PostgreSQL DBMS server:
Make sure that domain group support is enabled. When working with domain groups, access permissions are granted to DBMS users included in the group without explicit adding of each account in the security manager.
NOTE. Support of domain groups is available if there are groups as roles and users included in these roles on DBMS level.
Set up authentication based on GSSAPI method according to PostgreSQL documentation.
Make sure that the full path to keytab file is specified for the postgres service in the /var/lib/pgpro/ent-13/data/postgresql.conf configuration file:
# GSSAPI using Kerberos
krb_server_keyfile = '<path to keytab file for the postgres service>'
krb_caseins_users = on
Address of the postgresql.conf file may differ depending on DBMS version.
Set up use of full domain user name if required. By default, when a domain user is added to PostgreSQL DBMS, a short user name without domain is used. To use full name, set the USEUPN parameter to True in the file /opt/foresight/fp10.x-biserver/etc/Metabases.xml:
<LogonData ... USEUPN="true"/>
Restart the DBMS server.
After executing the operations the DBMS server is prepared.
Step 5. Setting Up Browser
NOTE. When setting up domain authentication skip this step.
To set up browser, enable the server and allowed nodes or local network, for example:
In Google Chrome add the AuthNegotiateDelegateAllowlist string parameter in the registry key [HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Google\Chrome] and specify the list of servers, for which the browser can give user credentials.
In Mozilla Firefox set the http://,https:// value for the parameters: network.negotiate-auth.delegation-uri, network.negotiate-auth.trusted-uris. The parameters are contained in the list at:
about:config
Step 6. Login
System login differs depending on the authentication type in use.
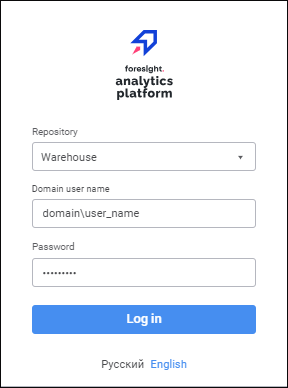
To log in to the system when domain authentication is used, execute operations in the login dialog box:
Select the repository used for domain users, enter domain user name in the format: domain\name and password.
Click the Login button.
To log in to the system when integrated domain authentication is used, click the Login In button in the login dialog box:
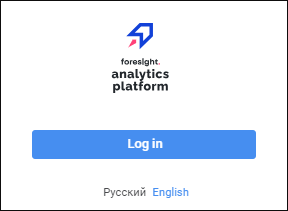
After executing the operations, domain user authorization is executed using the Kerberos authentication mechanism on DBMS side.